- Dynatrace Community
- Dynatrace
- Extend
- Extensions
- Automated Configuration Audit
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Pin this Topic for Current User
- Printer Friendly Page
Automated Configuration Audit
- Mark as New
- Subscribe to RSS Feed
- Permalink
31 Aug 2020 10:33 PM
We're happy to announce that we've open sourced our Automated Configuration Audit ActiveGate Extension for Dynatrace Managed/SaaS. Use it to automatically flow Dynatrace configuration changes directly into the UI for Applications, Hosts, Services, and Processes.
With IT moving faster than ever, the need to boost efficiency and drive productivity is a top priority. At the same time, navigating through modern IT infrastructures using APIs and various logs to find a specific event can seem like finding a needle in a haystack. Most Dynatrace environments contain thousands of monitored entities, keeping track of those configuration changes is cumbersome. The current approach is to manually extract the ID of the entity you want to see changes for, then pull the audit log via the API. Afterwards you must sift through the log for any events where you want to audit changes for. This process isn't scalable, and most importantly time-consuming. Keeping track of all your configuration changes within your Dynatrace environment is now automated for all your monitored entities using the Automated Configuration Audit ActiveGate Extension.
Benefits of using the Automated Configuration Audit ActiveGate Extension:
- Gain observability into configuration changes in Dynatrace
- Eliminate the need to manually use the API
- Minimize mean time to detect and repair configuration changes
- Shift-right using automation providing more meaningful context information
- Optimized process for auditing logs decreasing expenses and time
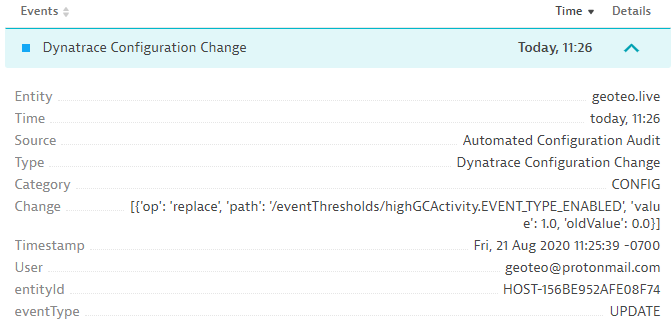
To put this all into context here is a screenshot of the ActiveGate Extension at work in a Dynatrace SaaS Environment. Here we can see the Events dashlet on the Host view where a change was done this morning at 11:26 AM. I enabled anomaly detection for high garbage collection on this host. Typically the time to get this information would be 30 minutes, and now it's instant. Providing insight into exactly who made what change and when. For Dynatrace Managed we also provide a link to the user in the Cluster Management Console. The best part is this information is now provided automatically with no manual effort.
Dynatrace clients now have access to meaningful configuration information shown directly in the context of whatever view they are looking at in Dynatrace, whether it be an Application, Host, Service, or Process. Enabling them to track all configuration changes in their monitoring environment. Clients are now able to shift-right using automation with increased collaboration, observability, and decreased mean time to detect and repair.
To view and download the extension please visit our GitHub repository. For any questions on the Automated Configuration Audit ActiveGate Extension, please reach out to George Teodorescu and Aaron Philipose.
- Labels:
-
activegate
-
extensions
- Mark as New
- Subscribe to RSS Feed
- Permalink
02 Sep 2020 02:22 PM
This is OUTSTANDING!
Out of curiosity, will this eventually be added to the core of Dynatrace itself rather than by extension? I think there is tremendous value in this. It seems to go along with the posts asking for an audit log viewer right inside Dynatrace rather than depending on the API.
Thanks!
- Mark as New
- Subscribe to RSS Feed
- Permalink
11 Sep 2020 08:03 PM
I got around to testing this today. I do not think this will work on ActiveGates that are running on Windows. If you goto the GitHub location you will find that the "README.md" shows the following:

However, if you install this and attempt to configure, you will receive the following error:

To my knowledge, this is due to the fact that there is no "tzset" in Windows and only will work on Solaris or Linux. A look at the docs on python.org shows the following:
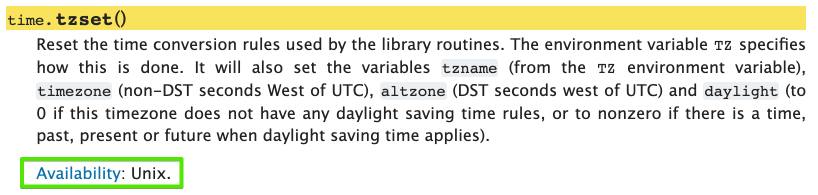
Reference: https://docs.python.org/3/library/time.html#time.tzset
While this extension is not officially supported by Dynatrace, I thought I would leave this comment for those that might try to use it on an ActiveGate running on Windows and attempting to figure out why it is not accepting the timezone.
- Mark as New
- Subscribe to RSS Feed
- Permalink
14 Sep 2020 01:25 PM
I noticed that for changes on synthetic monitors the event doesn't contain much useful info and always looks similar to this:

- The change value always has path "/publicInfrastructureSynchronizationTimestamp" with changing timestamps for "value" and "oldValue" no matter what setting was changed for the monitor.
- The user "SyntheticRestApiMonitorsDataPeriodicWorker" appears to be some internal technical user.
Could this be improved so the event contains useful info as well as the actual user that was responsible for the change?
- Mark as New
- Subscribe to RSS Feed
- Permalink
14 Sep 2020 04:36 PM
Anyone can improve on it as it is now open source. Depends on who has time for it 🙂
- Mark as New
- Subscribe to RSS Feed
- Permalink
15 Sep 2020 03:12 PM
FYI... I did hear back and it sounds like some updates will be made soon to it 🙂
- Mark as New
- Subscribe to RSS Feed
- Permalink
08 Jun 2021 07:38 PM
Hi there, if someone could help, I would be grateful. I'm trying this but I get the following error:
2021-06-08 18:24:00.350 UTC ERROR [Python][11744377138819341592][Detailed-Audit-Prod][140390468417280][ThreadPoolExecutor-0_13] - [set_full_status] list index out of range
Traceback (most recent call last):
File "/opt/dynatrace/remotepluginmodule/agent/plugin/engine.zip/ruxit/plugin_state_machine.py", line 336, in _execute_next_task
self._query_plugin()
File "/opt/dynatrace/remotepluginmodule/agent/plugin/engine.zip/ruxit/plugin_state_machine.py", line 670, in _query_plugin
self._plugin_run_data.plugin_instance._query_internal(**self._plugin_run_data.plugin_args)
File "/opt/dynatrace/remotepluginmodule/agent/plugin/engine.zip/ruxit/api/base_plugin.py", line 452, in _query_internal
return self.query(**kwargs)
File "/opt/dynatrace/remotepluginmodule/plugin_deployment/custom.remote.python.automated_configuration_audit/audit_activegate_plugin.py", line 186, in query
self.process_audit_payload(audit_logs)
File "/opt/dynatrace/remotepluginmodule/plugin_deployment/custom.remote.python.automated_configuration_audit/audit_activegate_plugin.py", line 161, in process_audit_payload
entityId = str(audit_logs[x]['entityId']).rsplit(maxsplit=1)[1]
IndexError: list index out of range
The configuration say it's ok
and the token is configured as instructed:
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
10 Nov 2021 03:15 PM
Apologies for the delay.
We typically only get notifications on our GitHub Page. Are you still having this issue?
- Mark as New
- Subscribe to RSS Feed
- Permalink
06 Oct 2021 09:23 PM
Looks like this one might be dead until the extension is updated.


