- Dynatrace Community
- Ask
- Open Q&A
- What is the rule behind the Windows System process group?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Pin this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
08 Oct 2018 02:57 PM
I would really like to be able to understand the rule behind the scenes for the Windows System process group. I have seen some other postings looking to break certain processes out of this process group (lsass.exe) but just a general understanding of hey we lump these processes because of "X" would be great to be able to communicate with my customers.
Solved! Go to Solution.
- Labels:
-
process groups
- Mark as New
- Subscribe to RSS Feed
- Permalink
12 Oct 2018 01:43 PM
Come on....nobody??? I guess i'll submit a support ticket...
- Mark as New
- Subscribe to RSS Feed
- Permalink
12 Oct 2018 04:55 PM
Hi Tommy
I think https://www.dynatrace.com/support/help/monitor/pro... will help you
Yos
- Mark as New
- Subscribe to RSS Feed
- Permalink
12 Oct 2018 06:05 PM
Definitely came across that link and while it is very helpful to understand how DT identifies processes and groups them, it doesn't provide the rule behind "What falls into the Windows System Process group".
- Mark as New
- Subscribe to RSS Feed
- Permalink
12 Oct 2018 06:32 PM
Hello Tommy,
They probably use the environment variables to assign processes into the Windows System Process group. In the below link it talks about customizing the grouping for Windows services and that is the method they suggest to do so.
https://www.dynatrace.com/support/help/monitor/processes/can-i-customize-how-process-groups-are-detected/
Thanks,
David Nicholls
- Mark as New
- Subscribe to RSS Feed
- Permalink
12 Oct 2018 07:38 PM
Thanks David, after reading that I was super excited to give it a shot. I'm specifically trying to break out a certain windows service, "Active Directory Domain Services" on our primary domain controller where I have an infrastructure only agent running. I went through the steps and added the variable in the registry and restarted the service but haven't seen anything break out. I do see that this host has a restart that's going to happen tonight so I'll let that happen naturally and see if, since it was a registry change, that perhaps it needed a reboot of the actual host.
I really appreciate the link.
-Tommy
- Mark as New
- Subscribe to RSS Feed
- Permalink
12 Oct 2018 07:58 PM
Glad to know it was able to help!
- Mark as New
- Subscribe to RSS Feed
- Permalink
13 Oct 2018 03:09 PM
Well, unfortunately from my testing the custom process group detection is not working and the final method that is explained if all else does not work is just not very clear what to do. It would be great if someone else in the community could give it a whirl.
Thanks, Tommy
- Mark as New
- Subscribe to RSS Feed
- Permalink
17 Oct 2018 12:14 PM
@Tommy N. did you create a process detection rule for the environment variable you created?
- Mark as New
- Subscribe to RSS Feed
- Permalink
29 Oct 2018 12:19 PM
I did but nothing ever showed. I even setup the rule and made the changes just prior to a scheduled reboot of the system so everything, registry wise, should have been fresh.
I need to give this another shot.
- Mark as New
- Subscribe to RSS Feed
- Permalink
29 Oct 2018 02:07 PM
Ok, ran through this again with no luck. Added registry entry on secondary domain controller that has lsass.exe running on it(NTDS service). Setup a process group detection rule looking for an environment variable equal to DT_CLUSTER_ID. Restarted the NTDS service. Nothing...
Also added a Process Group Monitoring rule looking for an exe running with name equatl to "lsass.exe". Restarted the process again....nothing.
- Mark as New
- Subscribe to RSS Feed
- Permalink
27 Dec 2018 02:52 AM
Hi all, just realized that I might also has to answer customer's question on this later in near future.
Any new idea or discoveries? The way I see it I can only customer based on port number (for example in this screenshot I know 3389 is for RDP)
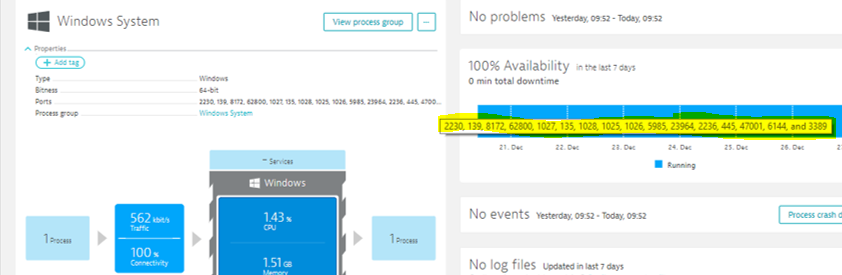
But then, I am not quite sure this way of looking at the listening port number is a verification approach or identification approach. It most fellow community member also get these ports numbers in their environment then we've got our answer.
- Mark as New
- Subscribe to RSS Feed
- Permalink
27 Dec 2018 09:05 AM
Do you need to split the processes on the listening port? This won't be possible as the process detection happens actually before the application even starts and listening sockets are created by the application itself.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08 Sep 2020
07:49 PM
- last edited on
16 Oct 2023
03:21 PM
by
![]() random_user
random_user
https://community.dynatrace.com/questions/182316/monitoring-infra-processes.html
Windows services, which are run under or started by svchost.exe (which is the case for most infrastructure services) are grouped into a special process group, called Windows System. It is not visible on the main host screen, but you should see it if you click the ‘All processes’ button.
Please note that there are exceptions from the above rule. For some selected processes, like IIS for example, we report them separately. However, it is not currently possible to configure which processes are added to Windows System group.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02 Mar 2023 04:30 PM - edited 02 Mar 2023 10:55 PM
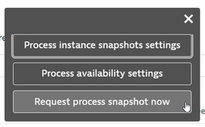
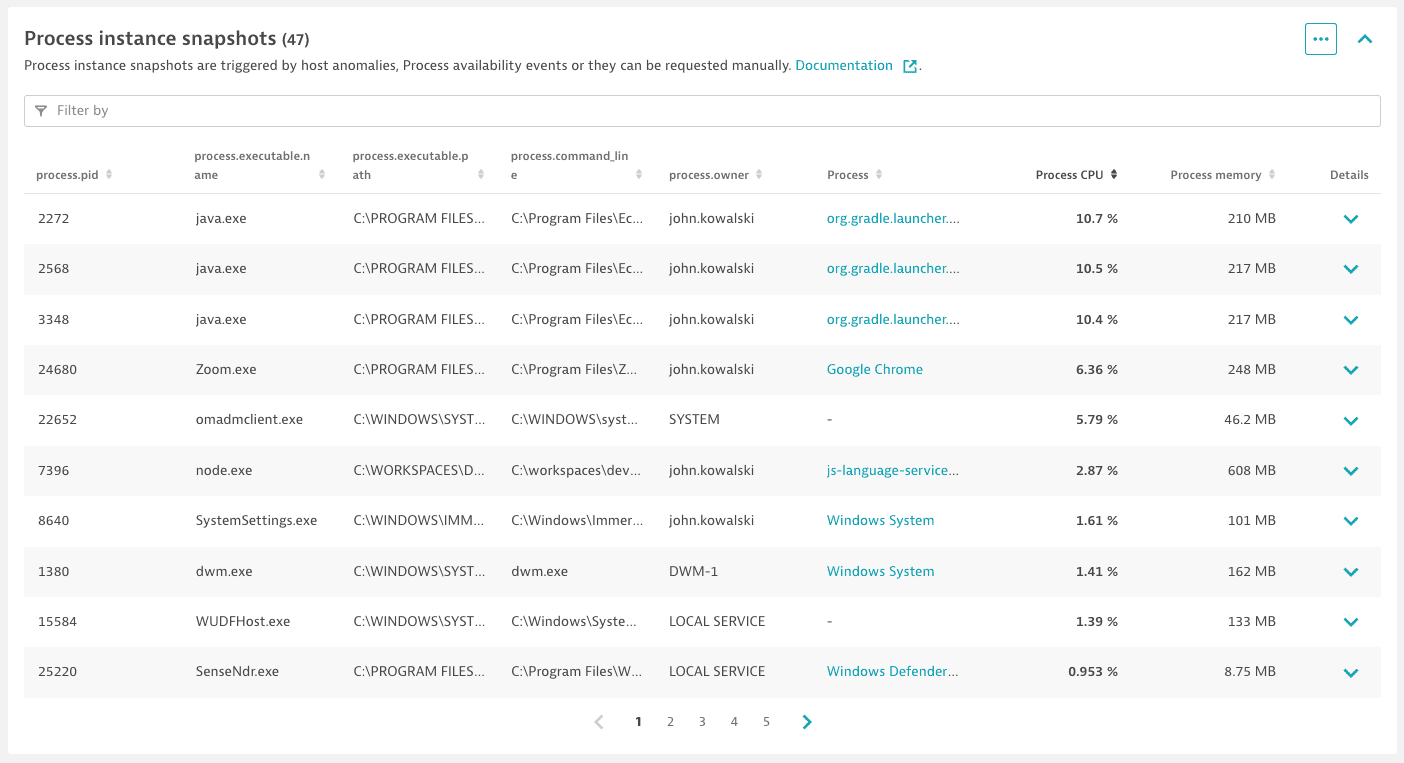
To get a more granular breakdown you can enable automatic process snapshots that run based on any of these triggering events or you can run a snapshot manually by selecting ... in the Process Snapshots section on a specific host page.
- High host CPU usage
- High host memory usage
- High packet drop rates
- High NIC utilization rates
- High number of NIC errors
- Process availability events
Featured Posts